THE LONG READ: From proving the existence of a seven-year-old girl in Syria to fact-checking locations of aerial bombings, how do you verify ‘open-source’ information in a war zone?
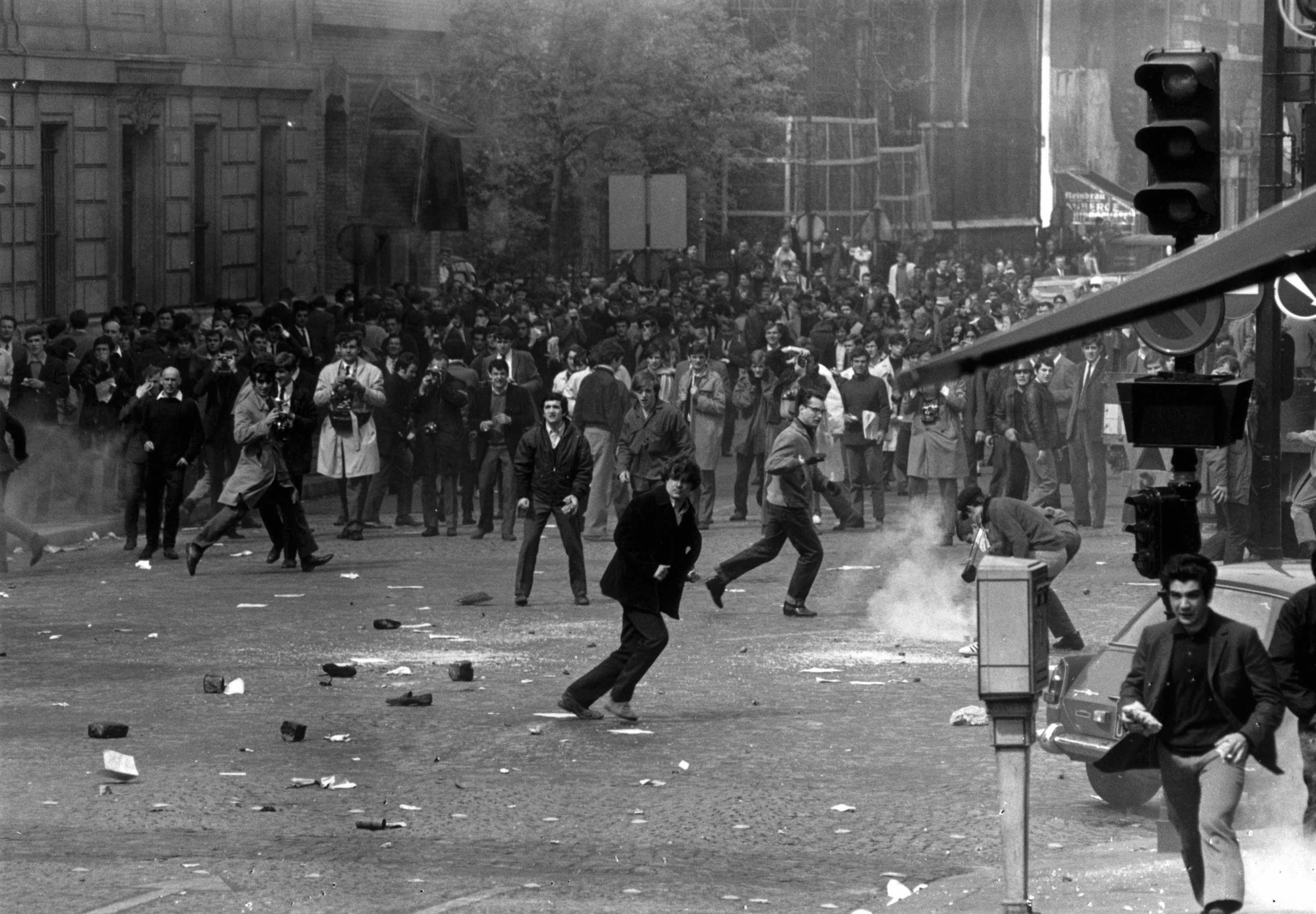
Truth, it has been said, is the first casualty of war. In the digital age, where anyone with a smartphone and internet access can produce and share stories at a fast pace, this thought is perhaps more relevant than ever.
On March 16, 2017, almost 300 people gathered for the Ishaa night prayers in the Omar ibn al-Khattab mosque south of al-Jinah, in northern Syria. At 6:55 PM local time, an airstrike targeted the religious complex, killing at least 38 individuals – according to claims made by locals.
How can a journalist seeking to establish what happened that night find out more while not being able to visit the targeted site? Online open source investigation offers an opportunity to discover, verify and validate multimedia information coming out of war zones. These can provide you with more elements to answer the who, what, when, why, where and how, and enable you to tell a story to your audience.
The information ecosystem in a conflict setting includes a great amount of propaganda as part of war strategy. At the same time, activists and citizens start playing relevant roles in reporting what is happening, especially now that they have the tools to do so and are easily able to connect globally.
Case in point: There are more hours of online video footage of the Syrian conflict than the actual time elapsed since the war began.
The increasing reliance on user-generated content (UCG) is in some cases the only information coming out of denied-access terrains for journalists. But this information may be biased or factually incorrect. Journalists, thus, need to have the skills and tools to go through the overwhelming amount of information produced during wartime, filter inaccurate information – whether published deliberately or not – and get the facts right.
This article aims to show how to verify UGC, with a specific focus on war and conflict contexts. The use of digital tools that facilitate reverse image search, checking the weather on a given location at a certain date and time, or geolocating a specific site, along with core journalistic skills, such as cross checking sources and interviewing relevant stakeholders, will be examined here as key elements of fact-checking.
First, a brief discussion about the importance of verifying photo and video, as a continuation of this introductory conversation is crucial to raise awareness on how easy it is to alter and/or decontextualise images, and how this in our visually driven world continues to be one of the main strategies used to misinform people.
Second, the best way to illustrate how valuable these verification resources and skills are, and show the diversity of situations they can be applied to in order to fact-check stories, is primarily done by examining four case studies where we have put them into practice. Finally, we describe the results they have rendered. Here are the four cases:
1. The United States (US) bombing of a mosque complex in northern Syria
2. Authenticating WhatsApp messages of Turkish coup plotters
3. Fact-checking locations of official videos: Russian airstrikes in Syria
4. Proving the existence of a 7-year-old girl in Aleppo
Photos and videos: Simple tools for verification
There are numerous examples of politicians and officials that use photos that were not related to the topic they were talking about. US Senator James Inhofe, for example, presented photographs to the Senate in February 2015 of what he said were Russian Army tanks in Ukraine the previous year. Two of the three images he showed were in fact taken during the 2008 Russo-Georgian War.That is not to say that there were no Russian Army tanks in Eastern Ukraine: Open source monitoring indeed shows there were.
More recently, Syria’s ambassador to the United Nations (UN), Bashar Jaafari, used an old photo taken in Iraq in an attempt to show the Security Council that Syrian government forces were not mistreating civilians in Aleppo.
The picture he used to corroborate this version of events appears to show a woman being helped down from a vehicle by a soldier, an image originally published in Arabic news websites in June 2016, describing it as a woman being helped by Iraqi soldiers in Fallujah.48 Ironically, Jaafari condemned the use of “fake news” around the December 2016 battle for Aleppo.
For images posted on the web, there is a simple tool to figure out whether it was posted before. This is called reverse image search, and browser extensions or add-ons have been developed by, for example, Google and TinEye, and can be downloaded for free. With two mouse clicks, you can see if an image was posted somewhere before the alleged event took place.
Here is an example of how useful reverse image search is used in verifying digital content. In the context of the increasing media coverage given to the recent flow of refugees seeking entry to the European Union, a photo of a boat loaded with people was being shared on social media, claiming to show refugees arriving in Europe in 2016. Some people reacted stating that they were not refugees in 2016, but European refugees arriving in northern Africa in the 1940s. Neither of the claims was true. A reverse image search shows the photo displays Albanian refugees arriving in Italy in 1991.
Even though an event may have happened, sharing photos that are not related to it may cause harm by people simply calling the whole event “fake” or saying it has not happened. This is especially relevant in a war context, where all involved parties and stakeholders will try to influence public opinion. Never forget that information is a crucial and powerful weapon.
Another good example of this is when, in May 2016, the White Helmets posted some photos that allegedly showed the aftermath of Russian airstrikes in a hospital in Idlib, Syria. One of the pictures they showed had appeared in a news piece by Al Jazeera in November 2015, which showed alleged airstrikes in Aleppo that, according to Syria’s Civil Defence, targeted residential areas and trucks loaded with humanitarian aid.
The Russian Embassy in the United Kingdom exposed the White Helmets through its Twitter handle, demonstrating they were using an image that did not correspond with the event they were referring to, and that it had been published months before.
Screen grab of the Twitter handle of the Russian Embassy in the UK, at the moment it exposed the White Helmets. On the left, the decontextualised picture can be seen on the bottom right of the tweet screenshot. On the right, a screenshot of Al Jazeera’s news piece, published in November 2015, that shows the same photo.
However, a reverse image search only does so much of the job. Searching for videos, for example, is significantly harder. Nevertheless, Amnesty International has developed a tool, the YouTube DataViewer, which allows you to find the exact uploading date and do a reverse image search of stills from the video. The latter may not always be accurate, but it is a good start for verifying videos. You may wonder why it is useful to know the exact uploading time, and why YouTube does not initially provide you with this information. It does tell you the date, but not the local time in which the video was published. An incident in which a suspected US airstrike killed civilians in Syria exemplifies why determining the uploading time of a video – local time – is crucial to having an accurate publishing date, and how both pieces of information are relevant to verifying news.
On a video uploaded to YouTube, a young girl can be seen amidst dust and twisted metal beneath the rubble of a destroyed building in Kafr Deryan, 40 kilometres west of Aleppo city in Syria. These images were among the strongest pieces of evidence pointing towards civilian injuries and casualties as a result of US-led Coalition airstrike in the early hours of September 23, 2014 – the first night of Coalition airstrikes in Syria. A thorough review of the content by Amnesty International, combined with satellite imagery analysis and reports by Syrian human rights groups, suggests multiple civilian deaths, raising the question as to whether this attack was proportionate and whether precautions to minimise harm to civilians may not have been taken. Yet, the US Central Command’s conclusion was unequivocal: “[…] Open source images presented as casualties from the strikes actually came from previous [Government of Syria] strikes.”
Now, the YouTube video may indeed cause confusion: It says it was uploaded on 22 September, but the uploading date reflects the time difference between Syria and US Pacific Time, where YouTube’s headquarters are based and used as the official publishing date. Ignoring this can easily lead to wrong research findings, as happened in the past, and may confuse reporters and journalists seeking to verify critical information.
Using Amnesty’s YouTube Data Viewer, it is possible to extract the exact time and determine local publishing time: Around 6:00 AM local time on September 23, which fits perfectly with the timeline of the attack. It is worth noting that organisations such as Amnesty International have gathered compelling evidence related to specific attacks by Coalition forces from 2014 to 2016, often using open-source material.
So far, we have shown relevant examples of how reverse image search and other tools allow journalists to check visuals within a few seconds. But how do we go about more difficult cases?
News verification can change the news
As a journalist, if you take the information that stakeholders are feeding you without verifying it – or any kind of information for that matter, especially in a war context – you are failing to do your job. Verifying news is pushing for accuracy, a core journalistic value, or at least aiming to do so. When we succeed, when we get the facts right, news verification can actually change the news: Establishing facts as a means to answer the W’s of journalism (who, what, when, why, where) and how events take place, might result in changing the story. Sometimes, despite all of our efforts, we cannot verify a piece of information – in which case it should be relayed to the audience as a means of ensuring utmost transparency.
The following case studies offer good examples of the possibilities and challenges of news verification.
The US bombing of a mosque complex in Northern Syria
To begin with, it is a matter of noticing something has happened. But if you are on the other side of the world, how can you notice a relevant incident, and how can you try to verify it? There are a number of ways for discovering events, and social media is today a relevant public space to access this information. Make social media monitoring a habit. There are a number of digital tools for this. One of them is TweetDeck, where you could start by putting together a list of activists, citizen journalists and any other gateway medium that may potentially be of interest. When looking for a specific geographical area, you could also try to find geotagged photos via services like EchoSec and WarWire.
On March 16, 2017, an airstrike hit a mosque complex in Al-Jinah, Syria. Locals tweeted only two minutes after witnesses stated they heard airstrikes. The first tweet mentioning a strike in al-Jinah, for example, was sent into the worldwide web at 6:57 PM local time – only two minutes later. The tweets published minutes after the incident from local citizens claimed that the village had been targeted by warplanes without specifying what or by whom. At 7:07 PM local time, a tweet mentioned that the airstrike was conducted by the Russian Air Force. Local media agencies echoed that claim. On YouTube, on the other hand, a steady stream of videos coming from the alleged targeted site would become available approximately 1.5 hours later. These videos were later assessed for their noteworthiness. The information came from different platforms like Twitter, Facebook, YouTube, in addition to media and other relevant websites. However, it may well be that these sources actually all refer to the same tweet, with or without mentioning it.
When you find your incident of interest, the next step is to collect every video, photograph, and any other relevant piece of information, and post them in one place to begin making sense of the incident. Wherever possible, identifying the original source of that information is key, as it allows journalists to:
1. Verify whether the content is new
2. Discover new information posted by the same source
3. Identify any links those sources may have that can take you to other potential sources
For example, in the mosque attack, we could identify the relevant YouTube channels quickly, and on the main page of those channels were other links to different social media channels. All this content is essential, as it may contain key information for the verification process. So, how can you track down the original source? If it is a photo, for example, you might want to try a reverse image search. If it is a claim, try searching Twitter on a keyword and list the results chronologically. The aim is to answer who tweeted it first. The next step is to geolocate as many of the images as possible, so you can begin to get a sense of the location, and start eliminating any videos or photographs that might not be relevant, or flag those that need further investigation. Geolocation is the exact determination of a location where a video was taken.
One challenge is that it is occasionally very tricky linking interior shots of a structure to its potential exterior, so we can prove the interior belongs to the structure we are examining. In the al-Jinah-case, a video filmed by a local inside the mosque complex and uploaded to YouTube not only allowed us to link the interior with the exterior, but also to confirm details about the building, such as the prayer room being below ground level, and connected to the outside by a staircase to the north side of the building. We compared the interior shown in the video with images showing the exterior, as well as satellite imagery obtained via Google Earth, Microsoft Bing Maps, and TerraServer. While the filmmaker’s interpretation of the evidence in the area cannot be verified, the details provided about the physical space are essential in understanding the incident.
Once you have obtained as much information as possible regarding available imagery through tools such as geolocation and reverse image search, you will start having a better understanding of the area, so when you come to review statements from locals gathered through social media you can compare them to what is visible within the geolocated images. Through that, you might also be able to make sense of some of the more unusual things you have noticed.
Back to the al-Jinah case, the first clue that the attack was by US or Coalition forces was the remains of munition reportedly recovered from the scene of the attack.
Journalist Sakir Khader obtained the photograph from one of his sources on the ground. Moments after the attack, he asked them to find bomb remnants on the scene and to take photographs and gather information that could lead to determine who had dropped them.
The label was near-identical to the labels used on Hellfire missiles, only used by the US and Coalition forces, so despite claims in some of the initial videos and tweets from the attack site that Syria or Russia were responsible, the evidence found in the photo pointed in a different direction.
That same night, the US Central Command claimed responsibility for the attack, wrongly stating its target was a location in Idlib, Syria. The geolocated images clearly showed it was in the Aleppo governorate, though close to the governorate borders. The Pentagon would later state, according to Bellingcat, that this may have been due to differences in internal reporting.
It was clear from the geolocated image that there was a massive crater on the north side of the large building in the complex, far beyond what a Hellfire missile could achieve. Based on witness accounts in videos posted on YouTube and Facebook, and text posts on Twitter, some claims seemed to explain this. Witnesses said that a larger bomb had been dropped, followed by several missiles. While there were small differences in how the witnesses described the events, the larger bomb or bombs and several missiles recurred in each of their accounts. Often, you will find witnesses giving differing versions of the same event, but usually not dramatically different. Nevertheless, those accounts always need to be compared to other evidence to build a clearer picture.
So, after we verified the location, and put together a clearer timeline of the events by cross-checking and comparing eye-witness testimony, there were still crucial questions that needed to be answered:
1. Can we confirm who is responsible?
Interestingly, the US usually publishes reports about the approximate location they are striking. And they happened to have published a report about striking what they said were Al-Qaeda militants in the Idlib province. The building we had geolocated was located in the Aleppo province, but only a few kilometres from the provincial border with Idlib. In combination with the photos of weapon remnants that we obtained through photos and videos uploaded by locals and local media, we decided to email the Pentagon for clarification. Did the Idlib strike refer to the al-Jinah strike? Yes, it did, they would reply.
2. What was the targeted building?
This is especially important in the mosque example as we have the US claiming the target were militants linked to Al-Qaeda, while people on the ground claimed they were civilians and members of a local religious group. With this we had to go back to previously discovered sources, see what information was being posted there, and compare it to images from the attack. Ideally, we would have images from before the attack, or even social media pages used by the victims. Groups like the Violations Documentation Centre and White Helmets will often provide details of the victims, and we can reach out to groups and individuals on the 106 Journalism in Times of War ground via social media. No evidence of the presence of an armed group could be obtained via open source information. However, this does not necessarily mean there were no Al-Qaeda operatives. A question that would reveal more interesting information will be discussed now.
3. Was the targeted building a mosque?
Revisiting the incident as new information became available, and using that to review, verify, and discredit claims and findings, was crucial to reporting on this particular issue. Often new satellite imagery will become available that shows more details of the area before and after the attack, or, as in the case of the mosque complex attack, the US provided imagery from just after the attack.
The image provided by the Pentagon showed the building after the strike, claiming it was a “partially constructed meeting hall” and that they “deliberately did not target the mosque at the left edge of the photo in order to minimise civilian casualties”.
However, open-source imagery, videos, satellite photographs, as well as survivor testimonies collected by Forensic Architecture and Human Rights Watch, strongly indicated the targeted building was also a mosque. An adhan speaker, used for the call to prayer, was discovered on pre-strike footage, besides the mosque sign already in place near the mihrab inside the building.
As showed here, news verification enables you to answer basic journalistic questions: What happened? Who is responsible? Where did it happen? When did it happen? How did it happen? In this particular case, as it sometimes occurs, the question as to why it happened remains ambiguous. Were there really individuals linked to Al-Qaeda present? Or do the locals speak the truth? That is something we have not been able to answer satisfactorily, but it is evident that the building hit was a functioning mosque.
The al-Jinah case exemplifies how verifying news and UGC can provide your audience with accurate information about a newsworthy event, a responsibility that might find a more complicated path amidst the information chaos generated by war and conflict. By using geolocation, comparison and cross-check of information coming from different sources (from witnesses to the countries involved, such as the US), we were able to build a solid picture of what happened on March 16, 2017.
Authenticating WhatsApp messages of Turkish coup plotters
Screen grab of a video that showed part of the Whatsapp conversation between Turkish coup plotters. The original uploader is unknown.
In the morning of the failed coup attempt in July 2016 in Turkey, a WhatsApp chat allegedly displaying a conversation between part of the coup plotters surfaced on social media. While it was being shared thousands of times, the question was: “Is the group conversation authentic?” Based on the transcript, partly provided by Al Jazeera Türk, each and every message was analysed to confirm the authenticity of the conversation.
“66th on its way” or “212 has been passed” – some of the messages included in the chat – may seem cryptic, but with some research ‘212’ appeared to refer to a big shopping mall in Istanbul, and by comparing number plates of military coup vehicles and a database of Turkish vehicle registration plates, it was possible to determine that ‘66th’ referred to the 66th Mechanised Infantry Brigade.
Subsequently, advanced searches on social media can be done, for example, to determine if military vehicles with the same number plate were spotted at the locations mentioned in the group app. In that way, each and every message was carefully analysed and triangulated with other open source material, resulting in an extensive reconstruction of the coup attempt in Turkey in July 2016.
Military vehicles used during the coup attempt revealed more information about the units taking part in the event, as the vehicle registration plates reveal their military unit. These units could be matched with mentions of units in the WhatsApp conversation: ‘196’ refers to the 2nd Armoured Brigade and ‘117’ to the 66th Mechanised Infantry Brigade, both part of the Turkish Land Forces’ First Army, 3rd Corps. [Photo: (left) Baz Ratner / Reuters; (right) Getty Images]
Again, to be sure that the photo indeed showed the location it was said to show, we used geolocation. Always remember to cross-reference visual clues in a given footage or photo with satellite imagery.
Fact-checking locations of official videos: Russian airstrikes in Syria
Since the start of their respective air campaigns in Syria, as well as in Iraq, both the US-led Coalition and Russia have published videos purporting to show their bombs targeting military objects. Information-wise, this is one of the peculiarities of war: Content that perhaps in a non-war situation would not be produced and published. Content projected and presented by military forces can be used to deter and threaten adversaries, as well as to gain legitimacy among and support from public opinion. Fact-checking the following official airstrike videos resulted in some interesting findings.
When the Russian military started bombing targets in Syria in September 2015, President Putin claimed that the purpose of the mission was to fight Islamic State in Iraq and Levant (ISIL). Initial reports of the Russian Defence Ministry (MoD) claimed that ISIL was the only target of Russian military activity. Yet crowd source analysis of the videos purporting to show those airstrikes, ironically published by the Russian authorities themselves, quickly revealed that specific claims they made were not correct, as illustrated by two examples below.
Triggered by the discovery of two videos of the Russian MoD claimed to be filmed in or near ISIL-controlled Raqqa were geolocated in sites over 100 km west of the city. Bellingcat decided to test these claims by launching a collaborative effort to use the Check59 platform to geolocate and collect additional information on these official videos. The results were remarkable.
Some videos were verified as being in locations matching the title and description of the videos, but many others gave inaccurate claims as to whose territory was targeted, or even totally wrong location.
A video posted on the Russian MoD’s YouTube channel, claims to be showing an airstrike on an ISIL “ammunition depot” in the Raqqa governorate.60 The Russian MoD implies that the strike occurred near Tabqa, west of Raqqa. However, as has been the case in dozens of other videos, the video was actually geolocated 115 km away near Al-Bab, in the Aleppo governorate. It is unclear why the Russian MoD claimed the wrong location: Both territories were held by ISIL at the time.
Other videos, however, claimed to show airstrikes against ISIL targets but were geolocated to areas where there is no known presence of the group – implying Russia targeted other rebel groups instead. An example is an airstrike said to have taken place in Raqqa according to the MoD, but was geolocated to Al-Lataminah in the Idlib province. While the location was classified by media outlets and activists as “rebel-held”, the claim that there was no ISIL presence could even be substantiated with the Russian MoD’s own information: Their map of territorial control presented at a press conference. By using this as an overlay in Google Earth with the geolocated airstrike videos mapped, it showed that not only this strike but many others were actually in non-ISIL held territories. Note that this is in 2015; at later stages Russia published more videos showing strikes on actual ISIL-held territory.
Second, the circles are geolocated airstrikes, green for a correct location by the Russian MoD and red for not a correct location.
Perhaps the most striking geolocated airstrike video was published in December 2015. The Russian MoD released a video of what it claimed to be an “airstrike against an oil refinery near Khafsa Kabir.” However, this “oil refinery” was actually a water treatment facility, “producing an average of 18 million litres of water daily,” according to the United Nations Children’s Fund (UNICEF) representative in Syria, Hanaa Singer. The structure shown in the airstrike video appears identical to Google Earth satellite imagery.
Further analysis of ground-level photographs of the facility confirmed this was indeed a water treatment facility, and not an oil-refinery as claimed by the Russian MoD. Additionally, using a file type search on Google, we obtained an official document of the German company that renovated the water treatment plant – providing further evidence that this was in fact a water treatment plant, and not an oil-refinery as claimed by the Russian MoD. These are all examples of how aerial views can be analysed against satellite imagery to establish facts. Now, geolocation is also useful to match a ground perspective to satellite imagery. This method has been used to proof the existence of a seven-year old girl in Syria, as our next and last case study will show.
Proving the existence of a seven-year-old in East Aleppo
As the Syrian government forces encircled the city of Aleppo in late 2016, a seven-year old girl named Bana Al-Abed gave a voice to many civilians trapped in the city’s opposition-held east. Helped by her social media savvy, English-speaking mother, Fatemah, Bana’s Twitter account published pictures of their daily life, amassing over 300,000 followers, including author of the Harry Potter series JK Rowling.
Bana’s rapid rise to world prominence soon made her a target in the online battle over alleged misinformation about Syria.
In an interview, Syrian President Bashar Al-Assad conflated Bana Al-Abed with “terrorists or their supporters” and suggested her Twitter account was a “game” and “propaganda”. Online critics questioned the remarkably well-written English of a seven-year old or why her house still had electricity and internet in besieged east Aleppo. As the speculation about her account became so prevalent, two Bellingcat volunteers decided to examine Bana’s Twitter account, effectively fact-checking the life of the seven-year old Syrian girl.
The open-source investigation used methods and tools such as social news gathering, context analysis, cross-reference of sources, geolocation, and satellite imagery, among others, to examine Bana’s existence and authenticity. For example, they were able to establish that Bana was indeed tweeting from East Aleppo, and not from Turkey, as some of her critics suggested.
The Bellingcat team used her videos and photos posted on Periscope and Twitter, including footage in which Bana herself appears, and geolocated them to the area around the same apartment block in East Aleppo where Bana claimed to live, using freely available satellite imagery from Google and Bing Maps. More recent satellite imagery also supported the claim that Bana’s family apartment was bombed on November 27, 2016.
Also, the team was able to determine several facts with regard to other claims:
1. By analysing Bana’s Periscope videos and reviewing news reports on her (from the BBC and Sept à Huit) they concluded that Bana and her family had access to electricity through solar panels installed on their roof. The panels allowed them to charge some form of car battery, which was then used to charge the phones.
2. As for the internet access, they examined tweets, news pieces, and reports from IT solutions company Dyn, to establish that there were multiple ways in which Bana and Fatemah could have gained access to the Internet.
3. As stated in Bana’s Twitter account, it was Fatemah, her English-speaking mother, who wrote a majority of tweets. Fatemah, in fact, had been clear and open about her running the account.
Photos and videos posted by Bana Al-Abed’s Periscope and Twitter accounts can be geolocated to a neighbourhood in East Aleppo using openly available satellite images. Online critics had earlier questioned whether the seven-year old girl was really in Syria, but actually tweeting from Turkey or somewhere else instead.
The district where Bana’s family home is located fell to the Syrian government and allied forces on December 3. Bana and her family were subsequently evacuated to an opposition-held area in the countryside of western Aleppo governorate in late December 2016, along with thousands of others displaced from east Aleppo.
You can do this!
In today’s world, where so much information is being shared, it is easy for inaccurate news to spread, especially on social media. Therefore, fact-checking, verification and validation of information coming out of war zones is more important and essential for the future of journalism than ever.
We have discussed how using open-source investigation, supported by digital tools and core journalistic skills, can help you search for stories and tell them accurately to your audience. A simple reverse image search will do when you are just trying to validate if a picture actually corresponds to the story that is being told, but other times, when trying to establish the who, what, where, why, when and how, you will have to approach the story in a more holistic way and this requires using several tools and skills to establish the facts.
The discovery process will see you through to the next step, the next claim or UGC that needs to be verified. In sum, these will point out which combination of tools and methods can be used for determining the authenticity of each specific ‘fact’. Always keep your mind open, question everything and be creative in the ways you approach the content to verify it. Your aim is to build a picture as clear as possible. And if you do not figure it out, always be honest to you audience: Say you simply do not know. Before you know it, you will be a true digital Sherlock.
Hadi Al-Khatib also contributed to this article, which first appeared in the AJMI publication, Journalism in Times of War